Ransomware Protection & Response Service
Stopping modern ransomware before it stops your business.
Prevent intrusion, contain spread, harden identity, and restore operations with an enterprise-grade ransomware defense program.
Overview
for CISOs, CIOs, CROs, IT Heads, and Business Continuity Leaders
AmbiSure delivers Ransomware-aaS as a continuous, measurable, and audit-ready program designed for regulated and high-availability industries.
Our service integrates preventive controls, early detection intelligence, response playbooks, identity hardening, backup validation, and board-level reporting, tailored for BFSI, Insurance, Pharma, IT/ITES, and Manufacturing.
We operate with a 24×7 enterprise delivery model across India, SAARC, and the Middle East aligned with ransomware threat patterns, CERT-In requirements, and business continuity needs.
Business Challenges
Double & triple extortion
- Modern groups steal data, threaten leak sites, and target executives for pressure.
Backups are targeted first
- Many attacks begin with disabling, corrupting, or encrypting backup infrastructure.
Identity compromise is the new weak point
- Attackers exploit compromised credentials, MFA fatigue, remote access, and privileged accounts.
Ransomware has become a board-governed risk
- Regulators track breach timelines, reporting discipline, and governance failures.
Lateral movement is faster than ever
- AI-assisted tools help attackers escalate privileges and deploy payloads in minutes.
CERT-In mandates 6-hour reporting
- Poor internal escalation delays create regulatory exposure and reputational risk.
Insurance expectations are rising
- Cyber insurers now demand proof of control maturity, segmentation, and tested incident response.
Features
AmbiSure delivers ransomware defense as a multi-layered, continuously validated protection program:
- Identity & Access Hardening
- Privileged Access Hygiene (PAH) assessments
- Shadow admin detection
- MFA resilience testing
- Password hygiene & leaked credential monitoring
- Endpoint & Server Ransomware Prevention
- Behavior-based ransomware blocking
- Application allowlisting
- Lateral movement detection (Kerberoasting, Pass-the-Hash, RDP misuse)
- Backup Integrity & Recovery Assurance
- Immutable backups validation
- Backup segregation checks
- Recovery-time benchmarking (RTO/RPO audits)
- Network & Segmentation Controls
- Internet-exposed asset audits
- Micro-segmentation recommendations
- Firewall rule hygiene & segmentation drift detection
- Threat Intelligence & Early-Warning Signals
- Dark web monitoring for credentials, access sales, and data leaks
- Zero-day ransomware variant alerts
- Sector-based threat briefings
- Ransomware Tabletop Exercises (TTX)
- Identity compromise TTX
- Backup corruption TTX
- Double-extortion decision-making TTX
- Boardroom crisis simulation
- Incident Response Playbooks & 24×7 Support
- Containment runbooks
- Forensic triage
- Communication templates for CERT-In & regulators
- Executive summaries for stakeholders
Value Proposition (Why this investment is justified)
- Reduced Probability of Ransomware Incidents
- Identity hardening plus continuous monitoring reduces intrusion pathways.
- Lower Impact of a Successful Breach
- Validated backups, segmentation, and containment runbooks reduce downtime and ransom pressure.
- Faster Detection & Containment
- Early-warning intelligence and behavior-based detection shrink the attack window.
- Stronger Audit & Insurance Defensibility
- Mapped evidence aligned to:
- ISO 27001:2022 controls
- SEBI CSCRF
- CERT-In 6-hour incident reporting rules
- DPDP safeguard obligations
- Mapped evidence aligned to:
- Clear Board-Level Visibility
- Quarterly resilience posture reports and risk heatmaps.
- Operational Efficiency
- Fewer high-severity incidents → reduced firefighting load on IT & Security teams.
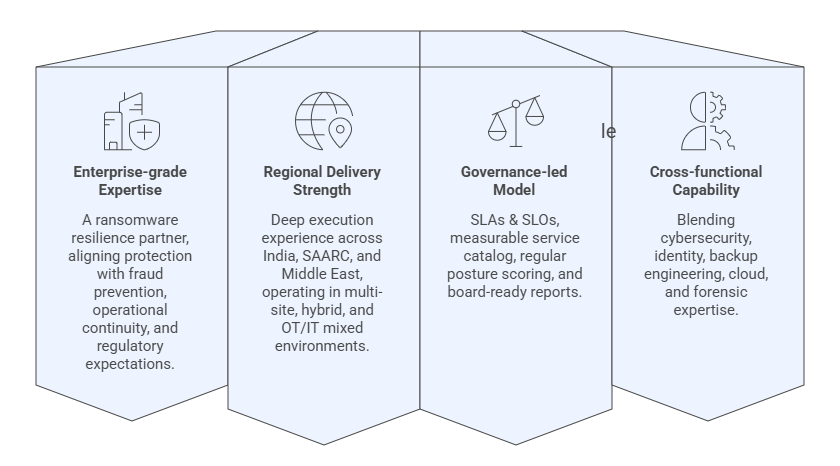
Why AmbiSure
WHAT OUR CLIENTS SAY
