Dark Web Monitoring (DWM) by AmbiSure
Uncover the Unseen. Act Before It’s Too Late. Detect Compromised Data. Prevent Identity Theft. Protect Brand Reputation.
Overview
Your Enterprise Data Is Already on the Dark Web—Do You Know It?
Cybercriminals don’t always attack your perimeter—they trade, sell, and leak your data on hidden networks long before a breach is publicly known.
For CISOs, CROs, and CIOs in BFSI, Pharma, Insurance, and Manufacturing, the question is no longer if your data is exposed, but where and how fast you can detect it.
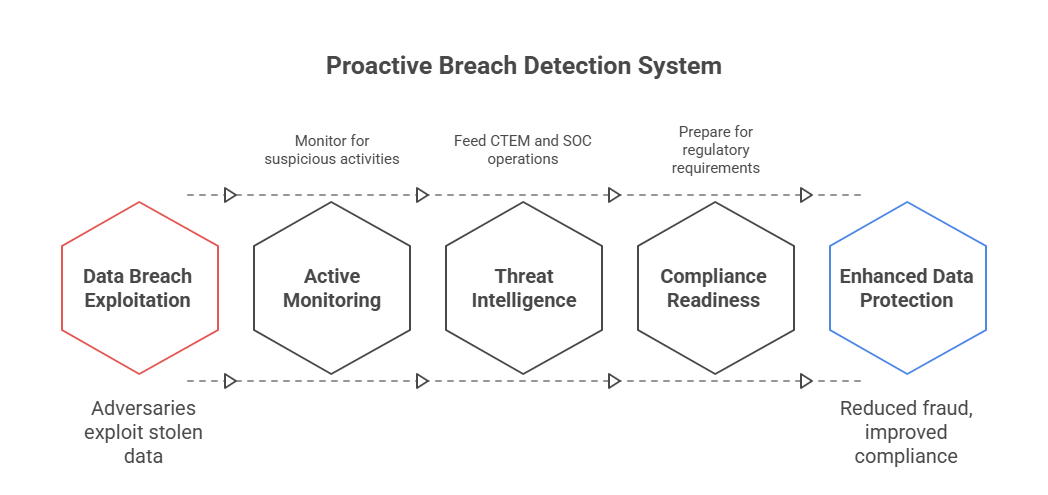
AmbiSure’s Dark Web Monitoring (DWM) gives enterprises real-time visibility into underground forums, marketplaces, and data leak sites, enabling proactive threat detection, credential protection, and brand defense—all integrated into your Cyber Threat Exposure Management (CTEM) framework.

The Challenge: Unseen Vulnerabilities
Data Leaks Before Detection
Sensitive data and credentials appear on dark web forums weeks before breach discovery.
Credential Theft & Account Takeover
Compromised employee or customer logins fuel phishing and fraud attacks.
Brand Impersonation
Threat actors launch fake domains and social accounts to deceive customers and employees.
Third-Party & Vendor Risks
Breaches in your supply chain expose your organization indirectly.
Regulatory & Compliance Pressure
RBI, SEBI, IRDAI, and DPDP Act require proactive data breach detection and reporting.
Reputational Damage
Leaked IP, trade secrets, or customer data erodes brand trust overnight.
Reactive Posture
Traditional SOC tools don’t monitor criminal marketplaces or underground channels.
What If You Could See What Hackers See?
A major private sector bank used AmbiSure’s DWM to identify leaked admin credentials and card BIN data posted on a dark web forum. Within hours, accounts were reset, customers alerted, and no financial loss occurred—preventing a potential ₹8 crore fraud and RBI audit incident.
FEATURES
DWM Features That Matter to You
Comprehensive Dark Web Intelligence
Continuous scanning across TOR, I2P, paste sites, Telegram, Discord, and deep web marketplaces for exposed data, credentials, and mentions of your brand or domains.
Compromised Credential Detection
Identifies leaked usernames, passwords, and tokens belonging to employees, executives, or partners.
Brand & Domain Monitoring
Detects typosquatted domains, fake mobile apps, or impersonated social media handles targeting your brand.
Data Leak Monitoring
Monitors for PII, PCI, PHI, financial records, and source code leaks linked to your organization.
Third-Party Breach Intelligence
Tracks vendor, partner, and supply-chain exposures impacting your ecosystem.
Automated Alerting & Risk Scoring
AI-driven prioritization based on severity, asset type, and potential business impact.
CTEM Integration
Feeds intelligence directly into your Cyber Threat Exposure Management cycle for validation, prioritization, and remediation.
Incident Response Integration
Seamless coordination with your MDR or IRP workflows to automate containment and reporting.
Geo-Specific Threat Feeds
Monitors India-centric underground markets, Telegram groups, and fraud networks for localized intelligence.
Regulatory Compliance Reporting
Prebuilt templates for RBI, SEBI, IRDAI, and DPDP data breach disclosure compliance.
business benefits
Business Value Delivered by AmbiSure IRP
Real-World Use Cases
BFSI
Detected card BIN leaks and phishing domains mimicking banking portals—prevented large-scale fraud.
Pharma
Found internal research data shared on dark web forums after a third-party vendor compromise.
Insurance
Identified customer data from a breached partner CRM—enabled rapid regulatory reporting and response.
Manufacturing
Discovered counterfeit product listings using brand name and logos; launched takedown actions.
Why Ambisure?

- Indian Regulatory Expertise: Native alignment with RBI, SEBI, IRDAI, and DPDP data protection requirements.
- Localized Intelligence Coverage: Tracks both global and India-specific dark web ecosystems.
- Integrated CTEM Approach: DWM is a core component of Cyber Threat Exposure Management, ensuring continuous risk reduction.

- Certified Threat Analysts: CERT-In empaneled experts validate and analyze every alert.
- Rapid Deployment: Go live in under 7 business days with domain and credential coverage.
- 24×7 Local SOC: Immediate alerting, validation, and response coordination.
- Strategic Advisory: Quarterly threat landscape reports and executive briefings tailored for CISOs.
WHAT OUR CLIENTS SAY
“AmbiSure DWM alerted us to leaked credentials on a Telegram group—before any fraud occurred. It’s our early warning system.”
— CISO, Leading Private Bank
“We detected leaked R&D data from a third-party compromise and acted before it hit media headlines.”
— Head of Cyber Defense, Pharma MNC
“The visibility into dark web chatter about our brand was invaluable. It helped us anticipate attacks before they happened.”
— CIO, Insurance Company
frequently asked questions
What is the “dark web,” and how does DWM monitor it?
- The dark web includes unindexed, encrypted parts of the internet (TOR, I2P). AmbiSure DWM continuously scans these sources for leaked data and brand mentions.
Is it legal to monitor the dark web?
- Yes. AmbiSure uses ethical, non-intrusive collection methods that comply with global and Indian cyber laws.
How often are scans performed?
- Monitoring is continuous and real-time, with immediate alerts for critical exposures.
What kind of data can it detect?
- Credentials, PII, payment data, source code, and corporate email leaks.
Can DWM integrate with SIEM or SOAR tools?
- Yes. Integrates seamlessly with Splunk, Sentinel, Cortex XSOAR, ServiceNow, and AmbiSure’s CTEM suite.
Does it help with compliance audits?
- Absolutely. Reports align with RBI, SEBI, IRDAI, and DPDP breach notification guidelines.
Can DWM monitor our vendors or subsidiaries?
- Yes. Add partner domains or vendors to monitor their exposure too.
How fast can it detect a new leak?
- Typically within minutes of the data appearing on dark web or leak forums.
