Zero Trust Network Architecture by AmbiSure
Never Trust. Always Verify. Continuously Monitor.
Redefine Access. Minimize Risk. Achieve True Cyber Resilience.
Overview
Your Perimeter Is Gone—But Your Risk Remains
In today’s hyper-connected world, the corporate network perimeter no longer exists. Cloud workloads, hybrid users, APIs, and IoT devices have expanded your attack surface beyond control.
Traditional VPNs and static network defenses assume trust once inside—a fatal flaw attackers exploit daily through compromised credentials, insider threats, and lateral movement.
For CISOs, CIOs, and CROs in BFSI, Pharma, Manufacturing, and Insurance, the path forward is clear:
Adopt Zero Trust Network Architecture (ZTNA)—a model built on identity, device trust, and continuous verification, not implicit access.
AmbiSure’s Zero Trust Network Architecture (ZTNA) helps enterprises transition from legacy perimeter security to identity-centric, adaptive access frameworks, aligned with NIST 800-207 and RBI Cybersecurity Guidelines—delivering uncompromised security and business agility.

The Challenge: Unseen Vulnerabilities
Top Business Challenges We Solve
- Perimeter Collapse: Cloud migration, remote work, and third-party vendors have erased the traditional network boundary.
- Lateral Movement Risks: Once attackers breach the perimeter, they move freely through flat networks.
- Identity Sprawl: Multiple identity providers and legacy systems create unmanaged access pathways.
- Compliance Mandates: RBI, SEBI, IRDAI, and DPDP require strong access governance, continuous monitoring, and micro-segmentation.
- Legacy VPN Vulnerabilities: VPNs expose wide network access, creating high-value attack routes.
- Shadow IT & Cloud Exposure: Unmonitored SaaS and cloud assets expand the attack surface invisibly.
- Lack of Contextual Access Controls: Static policies cannot adapt to dynamic user risk or device posture.
What If You Could Make Every Access Request Verifiable and Context-Aware?
A global insurance major replaced its VPN infrastructure with AmbiSure ZTNA. Within 90 days, they reduced unauthorized access incidents by 98%, blocked 12,000+ risky login attempts, and achieved IRDAI compliance alignment for identity-based access governance.
Users enjoyed faster, seamless access—security strengthened, productivity soared.
FEATURES
Key Features That Matter to You
Identity-Centric Access Control
Access is granted based on user identity, device trust, location, and behavior—not network position.
Micro-Segmentation
Divide your environment into granular security zones—contain breaches, limit lateral movement, and isolate critical systems.
Adaptive Policy Enforcement
Continuously evaluate risk using AI-driven behavior analytics and adjust access dynamically.
Device Posture Validation
Assess device health, OS version, security patch status, and compliance before granting access.
Secure Access Without VPN
ZTNA replaces legacy VPNs with encrypted, per-application access tunnels that hide internal apps from the public internet.
Continuous Verification
Every session and transaction undergo real-time risk scoring for sustained Zero Trust enforcement.
Integration-Ready Architecture
Seamlessly integrates with IAM, PAM, Passwordless Authentication, EDR, SIEM, and SOAR platforms.
Cloud & On-Premise Agnostic
Supports multi-cloud (AWS, Azure, GCP), hybrid data centers, and OT/IoT environments.
Regulatory Compliance Frameworks
Mapped to RBI Cybersecurity Framework, SEBI Cyber Resilience Guidelines, IRDAI Circulars, DPDP Act, and NIST 800-207.
Visibility & Analytics Dashboard
Unified dashboard for user behavior analytics, policy violations, and compliance reporting.
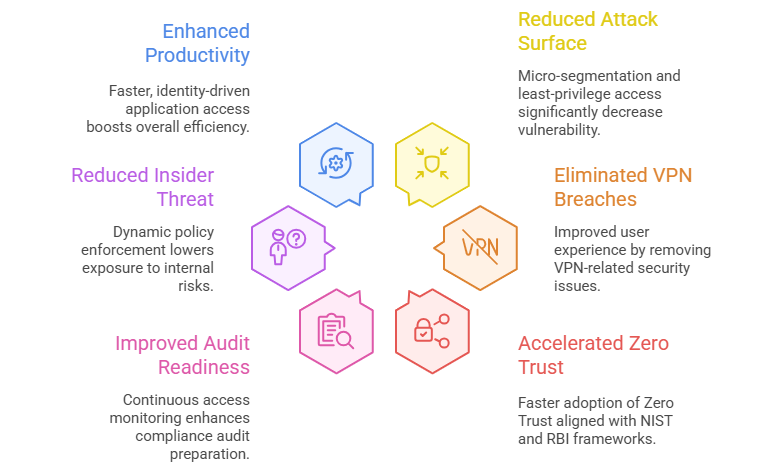
business benefits
Business Value Delivered by AmbiSure PAM
Real-World Use Cases
BFSI
Deployed ZTNA for remote employees and third-party vendors, ensuring RBI-compliant identity-based access.
Pharma
Protected R&D and GxP environments by isolating research systems with micro-segmentation.
Insurance
Replaced VPN with adaptive access, improving regulatory reporting and audit readiness.
Manufacturing
Implemented ZTNA for OT and IoT networks to prevent ransomware lateral spread.
Why Ambisure?
Strategic CXO Alignment
- We translate Zero Trust principles into board-level ROI and risk-reduction outcomes.
India Regulatory Expertise
- Tailored compliance mapping for RBI, SEBI, IRDAI, DPDP, and ISO 27001 frameworks.
End-to-End Implementation
- From assessment → design → deployment → monitoring, all handled by certified experts.
Technology Neutral
- Works across your existing firewalls, IDPs, EDRs, and cloud security tools.
Rapid Rollout
- Achieve Zero Trust baseline in under 45 days, with minimal disruption.
Local 24×7 Support
- CERT-In empaneled engineers and India-based SOC analysts ensure real-time coverage.
Zero Trust Maturity Advisory
- Our experts help you define a custom Zero Trust roadmap aligned to your digital transformation journey.
WHAT OUR CLIENTS SAY
“AmbiSure helped us transition from VPN to Zero Trust in under two months. Compliance improved, breaches dropped, and user experience skyrocketed.”
— CISO, Private Bank
“With AmbiSure ZTNA, we isolated R&D assets without disrupting workflows. True Zero Trust in action.”
— CTO, Pharma Giant
“Micro-segmentation and device posture validation stopped lateral ransomware movement entirely.”
— VP-IT, Manufacturing Leader
frequently asked questions
Is Zero Trust Network Architecture only for large enterprises?
- No. AmbiSure ZTNA scales for both mid-size and large organizations across on-prem, hybrid, and cloud setups.
Can it replace my VPN?
- Yes. ZTNA offers secure, identity-based, per-application access—eliminating the need for traditional VPNs.
Does it integrate with existing IAM and PAM tools?
- Absolutely. Works natively with Azure AD, Okta, CyberArk, BeyondTrust, and AmbiSure PAM.
How does ZTNA support RBI and DPDP compliance?
- By enforcing continuous access validation, adaptive authentication, and least-privilege principles mandated by regulators.
What about legacy applications?
- AmbiSure provides ZTNA connectors to secure access for legacy and non-web apps.
Does it work with cloud environments?
- Yes. Compatible with AWS, Azure, GCP, VMware, and Kubernetes environments.
How long does deployment take?
- Most enterprises see production readiness within 4–6 weeks.
What’s the ROI?
- Clients report 60% reduction in security operations overhead and 90% faster threat containment.
